In order to ensure the safety of public transportation, safety inspection has become a necessary means to ensure the safety of public life and property. However, due to high population mobility and large passenger flow, the demand and requirements for security inspection technology are also increasing. Because the traditional working methods of relying on manual inspection and image recognition cannot meet the needs of people when traveling, more and more modern intelligent technologies are applied in the field of security inspection.
At present, the combination of artificial intelligence and hardware has been implemented in many airport security inspection scenarios. Through data processing of various security inspection images, deep learning algorithms are used to realize automatic identification and early warning of contraband. In this way, the labor intensity of safety personnel is greatly reduced, the quality of safety inspections is improved, and adverse consequences caused by omissions and misjudgments of dangerous goods are avoided.
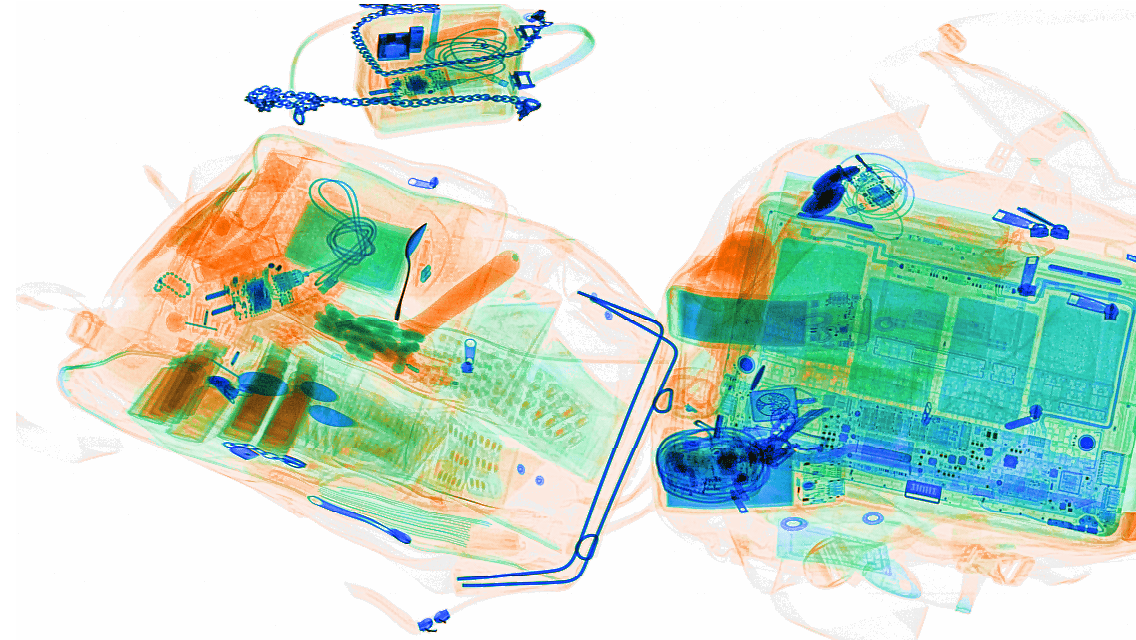
A set of target detection algorithms, data collection and calibration schemes specifically for X-ray security inspection images, and the development of corresponding software and hardware systems, which can be loosely coupled and docked with X-ray security inspection machines to realize the input, detection and output of X-ray security inspection images Complete system.
1. Algorithm flow design
The algorithm specifically designed for X-ray security inspection images is a two-stage target detection network, and a model suitable for X-ray security inspection image data is obtained by training the convolutional neural network. The input of this model is an X-ray image of a certain scale, and the output is the category, coordinates and confidence of the contraband in the image. The algorithm flow is as follows.
(1) The image processed by the capture card is sent to the feature extraction network while maintaining the original size after the edges are added and the average value is subtracted.
(2) The feature extraction network adopts a fully convolutional network structure and outputs feature maps.
(3) The feature map passes through the RPN, and the ROI of the region that may have a target is output.
(4) ROI produces a small-size feature map after pooling transformation, and then completes the classification and positioning offset calculation after passing through the Head network.
(5) The output deviation of the Head network is refined on the ROI, and the final prediction result is obtained, that is, the target detection result and the confidence level of the X-ray security inspection image.
The quality of the data determines the quality of the model. In order to train a model specifically for X-ray images, this model does not use conventional image data set training, but a large number of X-ray security inspection images with real contraband, and a combination of bags, fillers, and interferences. Combining the real packet data collected on site as training samples, and supplemented by multiple data enhancement methods such as color transformation, scale transformation, horizontal flipping and mirror flipping, and domain-adaptive image style transfer methods, millions of level The training samples cover the image characteristics of more than a dozen common domestic mainstream brand security inspection machines, making the model possess strong generalization recognition capabilities.

2. Hardware system structure and function
The hardware system design needs to carry the complete services of X-ray security inspection machine video signal access, X-ray security inspection machine EDID signal feedback, video signal amplification and distribution, video signal digitization, video image preprocessing, deep neural network reasoning and calculation, and rendering and display output.
The modules and functions are as follows:
(1) Video signal distribution module
(2) Video signal acquisition module
(3) Image processing module (CPU)
(4) Neural network computing module (GPU-1)
(5) Display rendering module (GPU-2)
-16310684285f80bb2942e434.jpg)
3. Physical display of the finished product
According to the hardware and software design, the finished prototype is shown in the figure. Screen display effect The target label display method is as different as possible from the pseudo-color image, and it has the least interference to the security inspector's line of sight.
Effective algorithms for X-ray security inspection images to detect and identify contraband objects, and implement software and hardware systems for actual security inspection scenarios. It can realize the complete process of X-ray security inspection image intelligent judgment, without any customized transformation of the existing X-ray security inspection machine. The system has been widely used in subways, high-speed rails, airports, logistics and other fields. In the future, by increasing the training samples of the targets to be detected, the types of recognition targets can be further expanded, and the recognition rate can be improved to meet the different needs of different application scenarios such as rail transit, logistics, airports, and customs. Effective, improve the quality of security inspection services, and have broad application prospects.
Continuous development of X-ray security inspection images-Safeagle
Fill out more information, We will get back to you within 24 hours.
4F.,Bldg. B, Jin Hao Pioneer Park, No.9 Dafu Industrial Zone, Aobei Community, Guanlan St., Longhua Dist., Shenzhen, R.P.China
Sales@Safeagle.com
Telephone : 86-0755-82373580
Business Phone : 86-0755-82373580
Work Time :9:00-18:30(Beijing time)